Cryptography is essentially important because it allows you to securely protect data that you don't want anyone else to have access to. It is used to protect corporate secrets, secure classified information and to protect personal information to guard against things like identity theft.
Today's post is basically going to be about cryptography, now before we actually jump into the main post, let me give you guys a brief on the topics that we're going to cover today.
So first of all, we're going to cover what is cryptography through the help of a very simplistic scenario.
Then we are going to go through the classifications of cryptography and how the different classificative algorithm books
What is Cryptography
I'm going to take the help of an example or a scenario to actually explain what is cryptography.
So let's say we have a person and let's call him Andy. Now suppose Andy sends a message to his friend Sam who is on the other side of the world.
Obviously he wants this message to be private and nobody else should have access to the message. He uses a public forum for example, the internet for sending this message. The goal is to actually secure this communication.
And of course we have to be secure against someone. Now, let's say there is a smart guy called Eve who has secretly got access to your communication channel. Since this guy has access to your communication. He can do much more than just eavesdrop. For example, he can try to change the message in itself. Now, this is just a small example.
What if Eve actually gets access to your private information? Well, that could actually result in a big catastrophe. So how can Andy be sure that nobody in the middle could access the message sent to Sam the goal here is to make communication secure and that's where cryptography comes in.
So what exactly is cryptography? Well cryptography is the practice and the study of techniques for securing communication and data in the presence of adversaries.
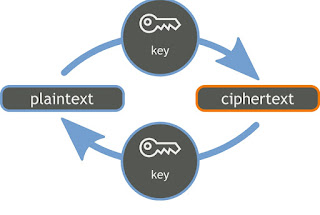
So let me take a moment to explain how that actually happens. Well, first of all, we have a message this message is firstly converted into a numeric form and then this numeric form is applied with a key called an encryption key and this encryption key is used in an encryption algorithm. So once the numeric message and the encryption key has been applied in an encryption algorithm, what we get is called a ciphertext.
Now this ciphertext is sent over the network to the other side of the world where the other person who the message is intended for, will actually use a decryption key and use the ciphertext as a parameter of a decryption algorithm and then he'll get what we actually sent as a message and if some error had actually occurred he'd get an error.
How Cryptography Secure Connection
So let's see how cryptography can help secure the connection between Andy and Sam.
So to protect his message Andy first converts his readable message to an unreadable form here. He converts the message to some random numbers. And after that he uses a key to encrypt his message after applying this key to the numerical form of his message, he gets a new value in cryptography. We call this ciphertext.
So now if Andy sends the ciphertext or encrypted message over communication Channel, he won't have to worry about somebody in the middle of discovering the private message.
Even if somebody manages to discover the message. He won't be able to decrypt the message without having a proper key to unlock this message. So suppose Eve here discovers the message and he somehow manages to tamper with the message and message finally reaches Sam. Sam would need a key to decrypt the message to recover the original plain text.
Using the key he would convert a ciphertext to numerical value corresponding to the plain text. Now after using the key for decryption what will come out is the original plain text message or an error, now this error is very important. It is the way Sam knows that message sent by Andy is not the same as the message that he received.
So the error in a sense tells us that Eve has tampered with the message. Now the important thing to note here is that in modern cryptography, the security of the system purely relies on keeping the encryption and decryption key secret.
Classification of Cryptography
Based on the type of keys and encryption algorithms cryptography is classified under the following categories.
Cryptography is broadly classified into two categories namely
- Symmetric key cryptography and
- Asymmetric key cryptography popularly also known as public key cryptography
Symmetric key cryptography is further classified as
- Classical cryptography and
- Modern cryptography
Further drilling down classical cryptography is divided into two which are
- Transposition cipher and
- Substitution cipher
On the other hand modern cryptography is divided into
- Stream cipher and
- Block cipher
I'll broadly explain all these types of cryptography later. So let's start with symmetric key cryptography first.
Symmetric Key Cryptography
Symmetric key algorithms are algorithms for cryptography that use the same cryptography keys for both encryption of plain text and decryption of ciphertext, the keys may be identical or there may be some simple transformation to go between the two keys. The keys in practice represent a shared secret between two or more parties that can be used to maintain a private information link.
This requirement that both parties must have access to the secret key is one of the main drawbacks of symmetric key encryption in comparison to publicly encryption also known as asymmetric key encryption.
Symmetric key cryptography is sometimes also called secret key cryptography and the most popular symmetric key system is the data encryption standards, which also stands for DES.
Transposition Cipher
Next up, we're going to discuss transposition cipher. So in cryptography a transposition cipher is a method of encryption by which the positions held by units of plain text, which are commonly characters or groups of characters are shifted according to a regular system so that the ciphertext constitutes a permutation of the plain text that is the order of units is changed. The plain text is reordered.
Now mathematically speaking a bijective function is used on the characters position to encrypt and an inverse function to decrypt.
So for example, lets say, we have a message which says "meet me after the party", now, this has been carefully arranged in the encryption Matrix, which has been divided into six rows and the columns. So next we have a key which is basically 4 3 1 6 3 5 and then we rearrange by looking at the plain text Matrix and then we get the ciphertext which basically is some unreadable gibberish at this moment. So that's how this whole algorithm works.
On the other hand when the ciphertext is being converted into the plain text the plain text Matrix is going to be referred and it can be done very easily.
Substitution Cipher
Now, we are going to discuss substitution cipher, substitution of single letters separately simple substitution can be demonstrated by writing out the alphabets in some order to represent the substitution. This is termed a substitution alphabet.
The cipher alphabet may be shifted or reversed creating the Caesar and upstaged cipher respectively or scrambled in a more complex fashion, in which case it is called a mixed alphabet or deranged alphabet.
Traditionally mixed alphabets may be created by first writing out keyword removing repeated letters in it. Then writing all the remaining letters in the alphabet in the usual order.
Traditionally the ciphertext is written out in blocks of fixed length omitting punctuations and spaces. This is done to help avoid transmission errors to disguise the word boundaries from the plain text.
Now, these blocks are called groups and sometimes a group count that is the number of groups is given as an additional check.
Now five letter groups are traditional as you guys can see that we have also divided our ciphertext into groups of five and this dates back to when messages were actually used to be transmitted by Telegraph.
Now if the length of the message happens not to be divisible by 5 it may be padded at the end with nulls and these can be any characters that can be decrypted to obvious nonsense. So the receiver can easily spot them and discard them.
Stream Cipher
Next on our list is stream cipher, a stream cipher is a method of encrypting text to produce ciphertext in which a cryptographic key and algorithm are applied to each binary digit in a data stream one bit at a time.
This method is not much to use in modern cryptography. The main alternative method is block cipher in which a key and algorithm are applied to block of data rather than individual bits in a stream.
Block Cipher
So now that we've spoken about block cipher, let's go and actually explain what block cipher does. a block cipher is an encryption method that applies a deterministic algorithm to the symmetric key to encrypt a block of text rather than encrypting one bit at a time as in stream ciphers.
For example, a common block cipher AES encrypts 128 bit blocks with a key of predetermined length. That is either 128, 192 or 256 bits in length.
Now block ciphers are pseudorandom permutation families that operate on the fixed size of block of bits. These PRPs are function that cannot be differentiated from completely random permutation and thus are considered reliable and been proven to be unreliable by some source.
Asymmetric Key Cryptography
So now it's time to discuss some asymmetric cryptography, asymmetric cryptography also known as public key cryptography is any cryptographic system that uses pair of keys, which is a public key which may be this emanated widely and private keys which are known only to the owner.
This accomplishes two functions authentication where the public key verifies that a holder of the paired private keys and the message and encryption where only the paired private key holder can decrypt the message encrypted with the public key and a public key encryption system. Any person can encrypt a message using the receivers public key that encrypted message can only be decrypted with the receivers private key.
So to be practical the generation of public and private key pair must be computationally economical. The strength of a public key cryptographic system relies on computational efforts required to find the private key from its paired public key. So effective security only requires keeping the private key private and the public key can be openly distributed without compromising security.
How Website is Secured Using Cryptography
So now that I've actually shown you guys how cryptography actually works and how the different classifications are actually applied. Let's go and do something interesting. So you guys are actually reading this post on this blog blueguard.ng right now.
So if you guys actually go and click on the secure part besides the URL, you can actually go and view the digital certificates that are actually used out here. So click on certificates and you'll see the details in the details tab.
Now as you guys can see the signature algorithm that is used for actually securing this website is being modern cipher suit AES_128_GCM, and this is a very very common encryption algorithm that is used throughout the internet.
Then the signature hash algorithm that is being used is AES_128_GCM which uses X25519 and the issuer is GTS CA 1D4 and you can get a lot of information about sites and all their authority, key identifiers, certificate policies, the key usage and a lot of thing about security just from this small little button out there.
If you all are still more interested, you all can actually research a lot on RSA. It's a very in-depth cryptography system. And also that brings us to the end of this session.
I hope you guys had fun learning about cryptography and the different methods that are actually used on the internet. That's it for me. Goodbye.
I hope you have enjoyed reading this post. Please be kind enough to share it and you can comment any of your doubts and queries and we will reply them at the earliest do look out for more posts in our content gallery and follow Blueguard website to learn more. Happy learning.
Bye.
Print this post


.png)

0 Comments